PhEmail简介
PhEmail是一款采用的Python编程语言开发的开源网络钓鱼邮件工具,它可以帮助研究人员在进行社会工程学测试的过程中自动化地给目标发送网络钓鱼邮件.PhEmail不仅可以同时向多个目标用户发送钓鱼邮件并识别出哪些用户点击了邮件,而且还可以在不利用任何浏览器漏洞或邮件客户端漏洞的前提下尽可能多地收集信息.PhEmail自带的引擎可以通过LinkedIn来收集电子邮箱地址,这些数据可以帮助测试人员完成信息采集阶段的一部分工作。
除此之外,PhEmail还支持Gmail的身份验证,这一功能在目标站点屏蔽了邮件源或IP地址的情况下会非常有用。值得一提的是,该工具还可以克隆目标组织或企业的门户网站登录界面,测试人员可以用这些伪造的页面来窃取目标用户的登录凭证。
使用样例
一般来说,第一步是收集目标企业的邮箱地址.PhEmail的搜索引擎在收集到了企业邮箱地址之后,会将它们保存在一个文件中,演示代码如下:
Gathering emails from domain: example.com100%
Completed!
[email protected]
[email protected] […] emails.txt updated
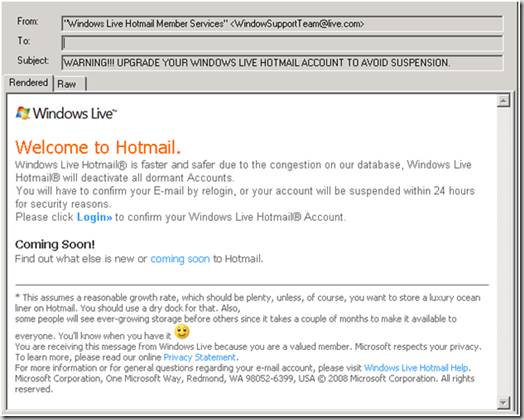
得到了企业邮箱地址之后,接下来就要创建钓鱼邮件模板了。模板中的每一个URL必须要包含一个字符串” {0}”,因为脚本会自动将这个字符串替换成正确的URL地址。一次真实的测试场景截图如下:

接下来,我们需要在网络服务器上安装PHP环境并将PHP文件”的index.php”复制到网络服务器的根目录下。这个文件中包含的JavaScript的代码会收集浏览器信息并将其保存到/ tmp目录目录。下的日志文件中演示实例如下:
# phemail.py -e test-emails.txt -f"Fast Holiday " -r "Fast Holiday " -s
"Last MinuteHoliday" -b body.txt -w http:SMTP server:
mail.example.com
Sent to [email protected]
Error: sending [email protected]
Phishing URLs point to http:Phemail.py log file saved:
phemail-log-12-07-2012_15-42.txt
接下来,你只需要等待目标用户点击钓鱼邮件,然后你就能够收集到目标用户的某些浏览器信息了:
Email: [email protected]
Date: Thu 12/07/2012 11:00:13
IP: 192.168.0.123
User Agent: Mozilla/5.0 (Windows NT 6.1;WOW64; rv:13.0) Gecko/20100101
Firefox/13.0.1 appCodeName: Mozilla appName:Netscape appVersion: 5.0 (Windows)
appMinorVersion: undefined product: GeckocookieEnabled: true cpuClass: undefined
onLine: true opsProfile: undefineduserProfile: undefined language: en-US platform:
Win32 systemLanguage:undefined userLanguage: undefined flash: Enabled Plugins:
Google UpdateShockwave Flash 11.3 r300 Google Talk Plugin Video Acceleratorversion:
0.1.44.16 Version 3.1.4.8140 5.1.10411.0 Adobe PDF Plug-In For Firefoxand Netscape
10.1.3 NPRuntime Script Plug-in Library for Java™ Deploy VmwareRemote Console and
Client Integration Plug-in BlackBerry WebSL Browser Plug-InBing Bar The plug-in
allows you to open and edit files using Microsoft Officeapplications Office
Authorization plug-in for NPAPI browsers
PhEmail项目主页
工具下载
你可以直接通过克隆PhEmail的GitHub的代码库来完成工具的下载:
git clone https:
工具使用
PHishing EMAIL tool v0.13Usage: phemail.py [-e ] [-m] [-f
] [-r ] [-s] [-b ]
-e emails: File containing list of emails(Default: emails.txt)
-f from_address: Source emailaddress displayed in FROM field
of the email (Default: Name Surname surname@example.
com>)
-r reply_address: Actual emailaddress used to send the emails
in case that people reply to the email
(Default: Name
Surname )
-s subject: Subject of theemail (Default: Newsletter)
-b body: Body of the email(Default: body.txt)
-p pages: Specifies number ofresults pages searched (Default:
10 pages)
-v verbose: Verbose Mode(Default: false)
-l layout: Send email with noembedded pictures
-B BeEF: Add the hook for BeEF
-m mail_server: SMTP mailserver to connect to
-g Google: Use a google accountusername:password
-t Time delay: Add deleaybetween each email (Default: 3 sec)
-R Bunch of emails per time(Default: 10 emails)
-L webserverLog: Customise thename of the webserver log file
(Default: Date time in format"%d_%m_%Y_%H_%M")
-S Search: query on Google
-d domain: of email addresses
-n number: of emails perconnection (Default: 10 emails)
-c clone: Clone a web page
-w website: where the phishingemail link points to
-o save output in a file
-F Format (Default: 0):
0- firstname surname
1- [email protected]
2- [email protected]
3- [email protected]
4- [email protected]
5[email protected]
6- [email protected]
7- [email protected]
8- [email protected]
9- firstname_
免责声明
请不要在没有得到目标用户事先同意的情况下实用PhEmail来进行测试,由使用者自身使用不当所带来的问题开发人员不承担任何责任,同时我们也对PhEmail所带来的损失概不负责,请大家妥善使用。
其他参考资料
1.https://www.dionach.com/blog/phemailpy-another-social-engineering-tool
2.https://www.dionach.com/blog/social-engineering-and-phishing-email-attacks
文章出处:FreeBuf
渗透测试工具
为渗透测试准备的10大黑客工具
巧妙破解某高级渗透测试工具